Anodot Breach Lessons: When Your Vendor Is the Vulnerability



Background
The recent breach of Anodot, an AI analytics platform acquired by Glassbox in November 2025, exposed a growing attack vector: SaaS supply chain compromise. Threat actors used stolen Anodot credentials to access 12+ Snowflake customer environments, bulk-extracting data and demanding ransom. Anodot connects to Snowflake via stored username/password or RSA key pairs, meaning a single vendor breach handed attackers direct access to customer data warehouses. No Snowflake vulnerability required.
This incident underscores that misconfigured integrations, stored credentials, and lack of continuous monitoring across third-party connections remain significant risk factors. This is where Reco's Dynamic SaaS Security capabilities provide added layers of protection inventorying third-party integrations, detecting anomalous access, and identifying exfiltration attempts before they escalate.
1. Third-Party Integration Inventory
The Risk Organizations often lack visibility into which third-party tools hold Snowflake credentials, what those tools can access, and whether they're still actively in use. In this attack, a Snowflake-only search returned clean — active Anodot integrations were only discoverable through Okta and Entra app data.
Snowflake Control Run SHOW INTEGRATIONS to audit all connected integrations.
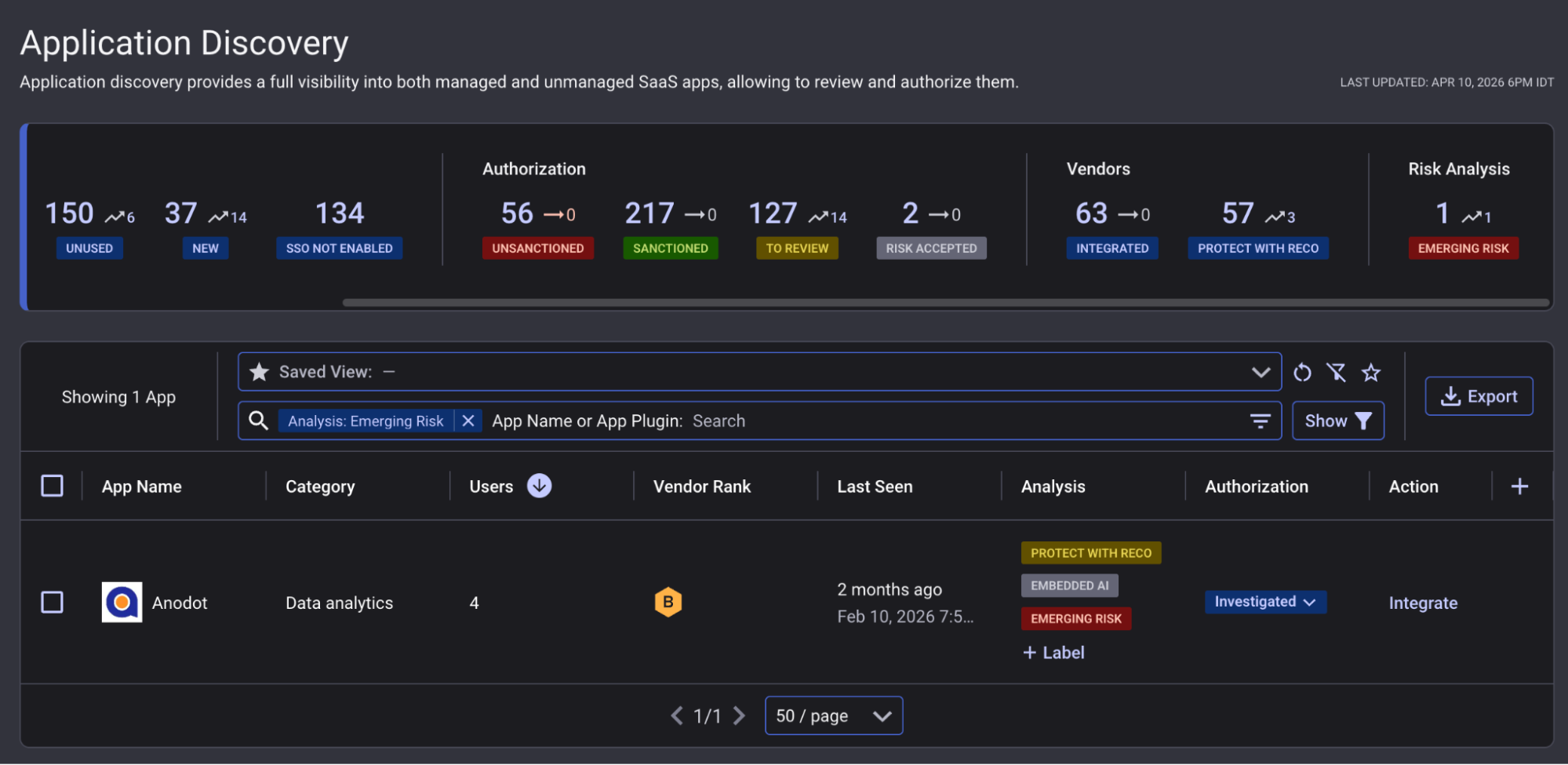
Reco Controls
- Posture Check — Third-Party Integration Inventory — surfaces all OAuth integrations per tenant, flagging non-standard connection types.
- Posture Check — Okta / Entra Third-Party App Inventory — cross-references IdP app registrations to surface integrations invisible to Snowflake-only audits.
When a vendor like Anodot becomes the subject of an active breach, Reco automatically applies an “Emerging Risk” label to flag it across your app inventory, so security teams know immediately whether that vendor exists in their environment and who is using it without waiting for a manual investigation.
In the Anodot incident, this is exactly the visibility gap that slowed initial exposure assessment. A Snowflake-only search returned clean. It took six rounds of increasingly deep investigation across Okta, Entra, enriched app data, and email logs to surface the full picture. Application Discovery would have surfaced Anodot on day one.
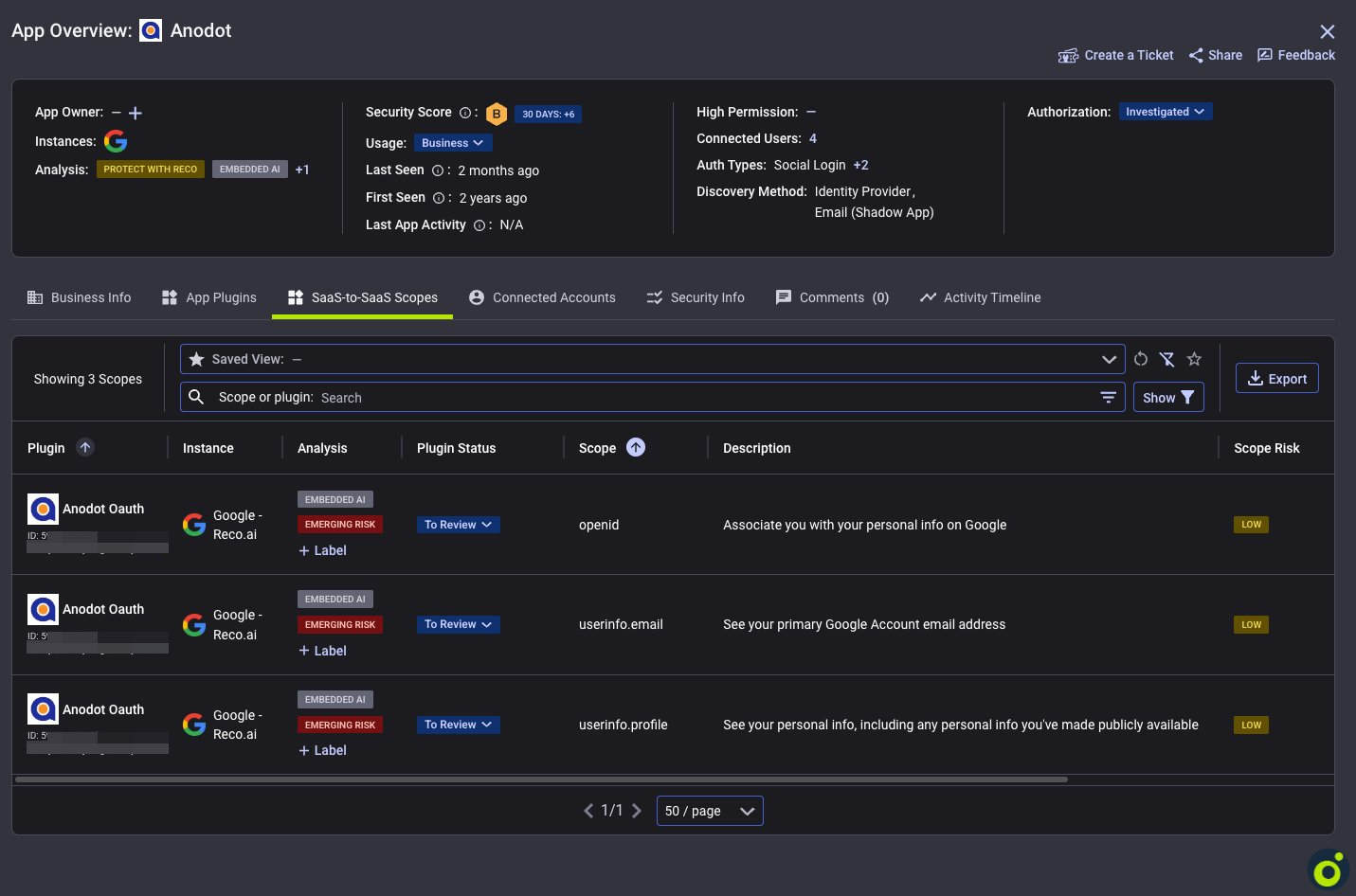
From the App Discovery view, teams can drill into the OAuth permissions and scopes each app holds making it immediately clear what data access a vendor like Anodot had and which users were connected.
2. Bulk Data Export Detection
The Risk: Standard Snowflake exfiltration monitoring catches data sharing CREATE SHARE commands that expose data to other Snowflake accounts. But that's not how large-scale data theft actually works. The real exfiltration mechanisms are COPY INTO and UNLOAD. These are Snowflake's native bulk export commands that write directly to external cloud storage like S3, GCS, or Azure Blob. In the Anodot breach, attackers had full query access to customer Snowflake environments via stolen credentials. With COPY and UNLOAD at their disposal, terabytes of data can leave the environment in minutes and most Snowflake configurations won't generate a single alert.
Snowflake Control Monitor QUERY_HISTORY for bulk export query types.
Reco Control
- Alert — Bulk Data Export to External Stage Detected — fires on COPY and UNLOAD query types combined with byte-volume thresholds, filtering out service account noise.
3. SSO Bypass and Login Anomaly Detection
The Risk: Anodot authenticates to Snowflake via stored username/password which is completely outside SSO. This is the core danger of third-party integrations: they often hold standing credentials that bypass every identity control your organization has invested in. When those credentials are stolen, attackers walk in through a door that SSO, MFA, and conditional access policies were never designed to guard. Reco closes this gap by detecting both the bypass itself and the authentication anomalies it produces.
Snowflake Control Enforce SSO for all accounts and monitor LOGIN_HISTORY for auth method anomalies.
Reco Controls
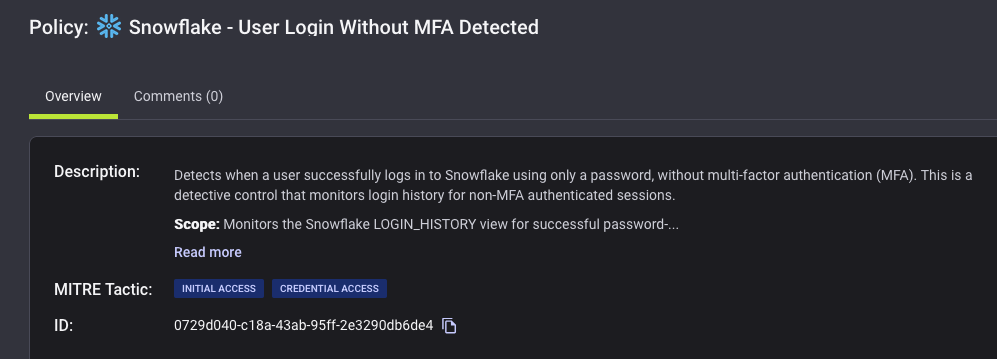
- Alert — SSO User Password Sign-Ins — fires when a password login occurs for an SSO-configured user.
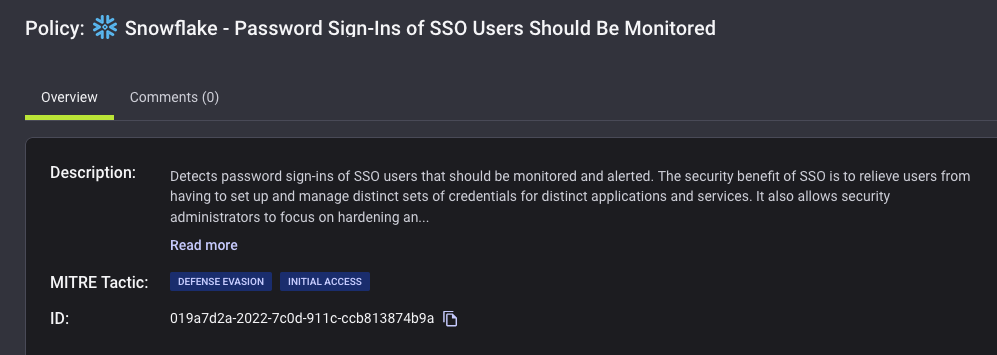
- Alert — Login Without MFA — fires on any successful login that bypassed MFA.
4. OAuth Token Login Monitoring
The Risk Third-party integrations authenticating via OAuth can go unmonitored if the authorizing integration is unknown or unexpected. Compromised integrations may use OAuth tokens to access Snowflake without triggering standard credential alerts.
Snowflake Control Monitor LOGIN_HISTORY for FIRST_AUTHENTICATION_FACTOR = OAUTH_ACCESS_TOKEN.
Reco Control
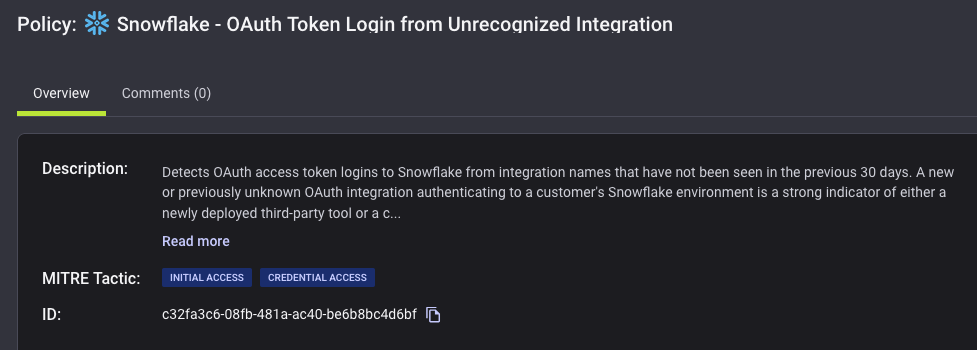
- Alert — OAuth Token Login from Unrecognized Integration — correlates OAuth logins against AUTHORIZING_INTEGRATION_NAME to detect access from unrecognized or unauthorized integrations.
5. New Client Application Detection
The Risk Attackers using stolen credentials rarely use the same client tooling as legitimate integrations. Unfamiliar client applications appearing in LOGIN_HISTORY are a strong signal of unauthorized access.
Snowflake Control Monitor REPORTED_CLIENT_TYPE in login history for unexpected values.
Reco Control
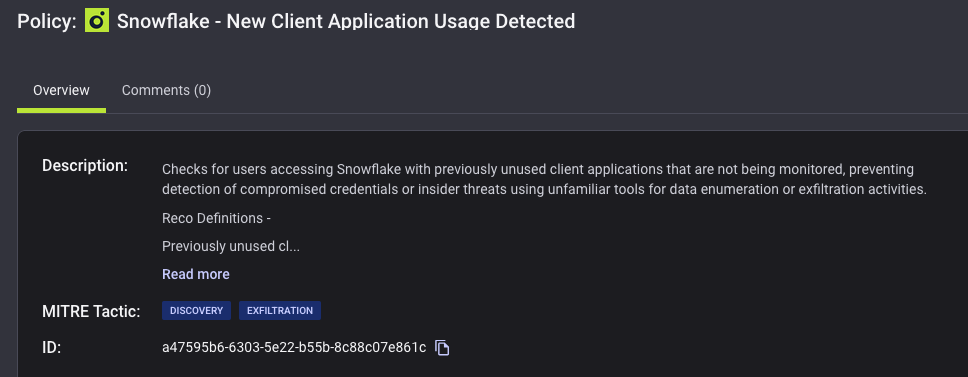
- Alert — New Client Application Usage Detected— detects client applications not previously seen in the environment.
6. Query Volume Anomaly Detection
The Risk Bulk exfiltration produces query volumes far outside a user's normal behavior — a pattern that's invisible without a behavioral baseline.
Snowflake Control Monitor QUERY_HISTORY for unusual per-user query volumes.
Reco Control
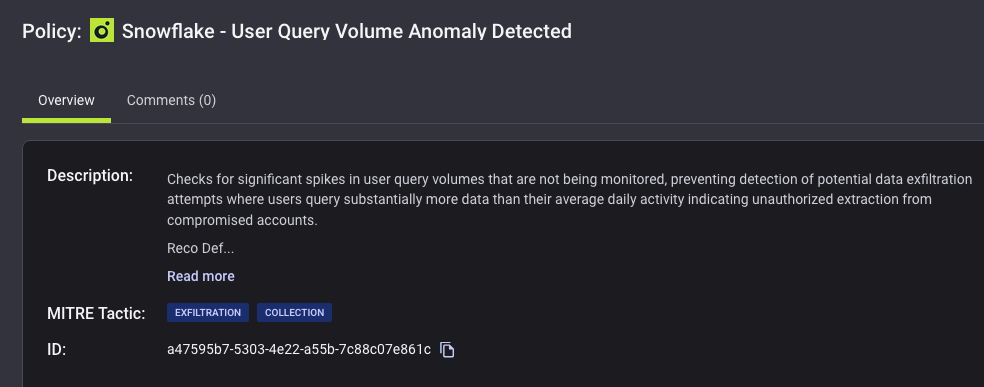
- Alert — Query Volume Anomalies — compares per-user query volume against a rolling weekly baseline, firing when activity spikes significantly beyond normal.
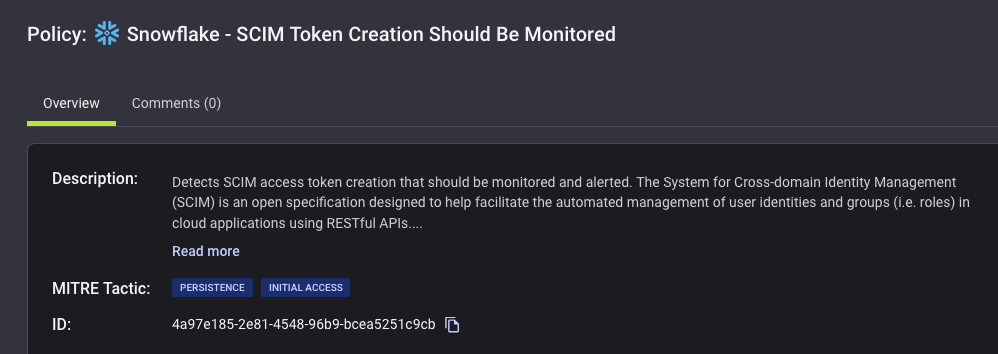
7. Persistence Detection
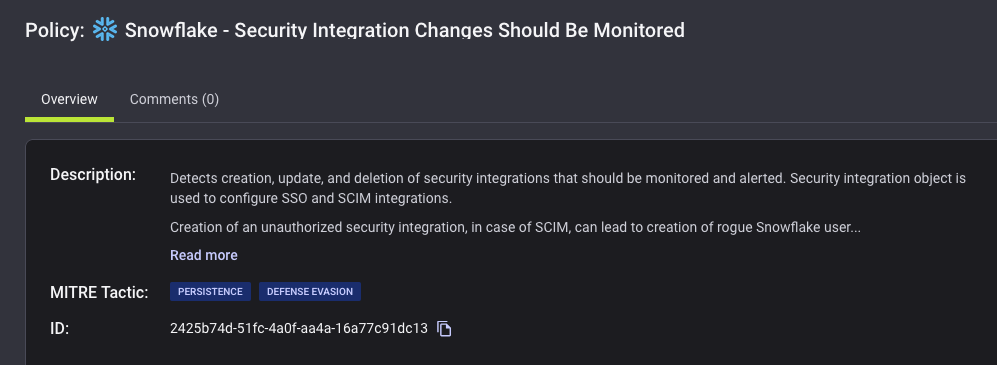
The Risk: Stealing credentials is just the beginning. Sophisticated attackers establish persistence so they survive credential rotation creating rogue security integrations to redirect authentication flows, or provisioning SCIM tokens to maintain programmatic access. Without monitoring for these changes, rotating the original compromised password gives a false sense of security while the attacker retains access through a backdoor.
Snowflake Control Monitor for unauthorized changes to security integrations and provisioning tokens.
Reco Controls
- Alert — Security Integration Changes — fires on any CREATE, ALTER, or DROP of a security integration.
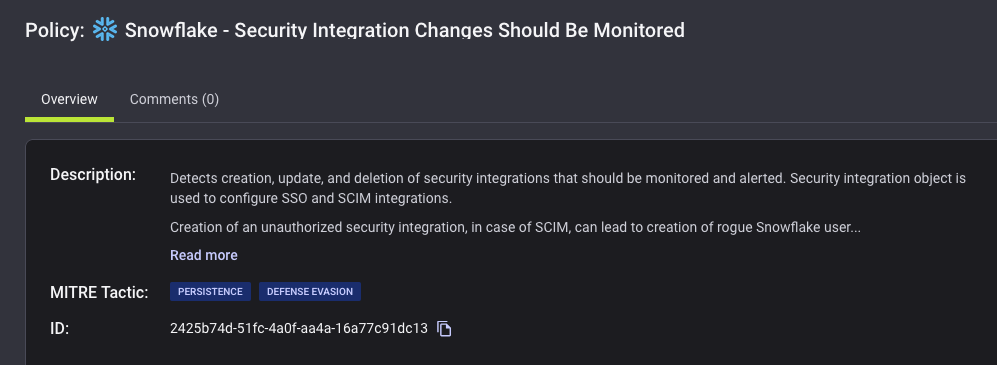
- Alert — SCIM Token Creation — fires when a new SCIM provisioning token is created.
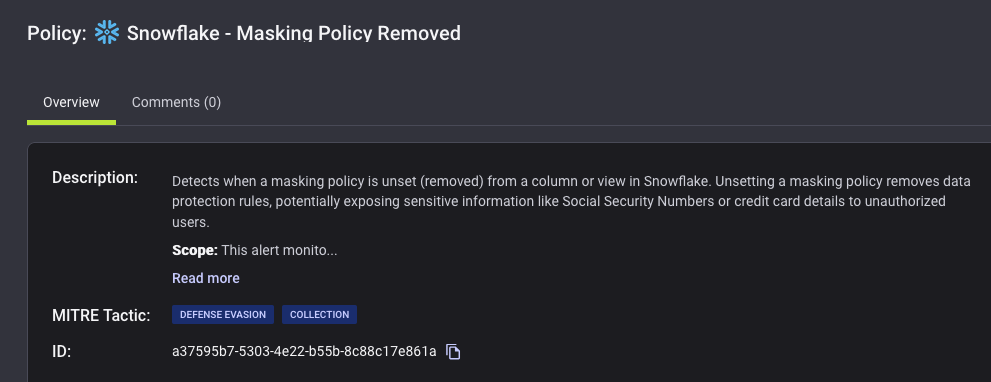
8. Pre-Exfiltration: Masking Policy Removal
The Risk: Data masking is often the last line of defense for sensitive fields such as names, SSNs, financial data. Attackers who've gained access know this, and removing masking policies before exfiltration ensures the stolen data is unredacted and immediately monetizable. This step often happens in the window between initial access and bulk export. Making it a critical early warning signal.
Snowflake Control Monitor for masking policy changes before data access events.
Reco Control
- Alert — Masking Policy Removed — fires when a data masking policy is dropped, signaling potential preparation for exfiltration.
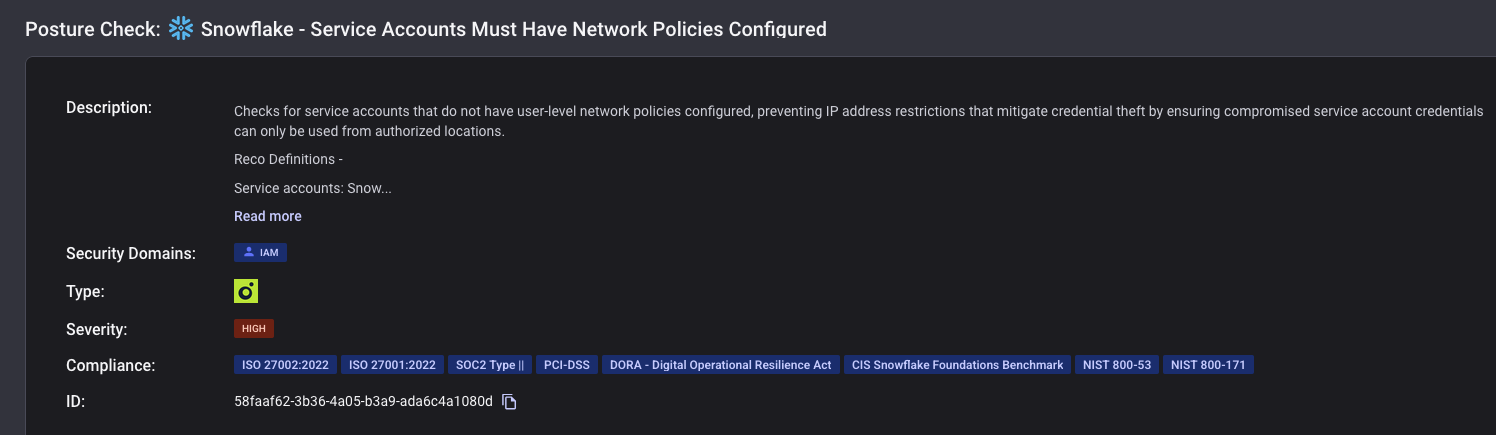
9. Service Account Network Policy Enforcement
The Risk Service accounts without IP restrictions can be accessed from anywhere — meaning stolen credentials are immediately exploitable regardless of the attacker's location.
Snowflake Control Enforce network policies on all service accounts to restrict access by IP range.
Reco Control
- Posture Check — Service Account Network Policy — flags any Snowflake service account lacking a network policy.
Summary & Next Actions
The Anodot breach is a stark reminder that attackers don't need to compromise Snowflake directly. They only need to compromise something connected to it. With Reco, organizations can go beyond Snowflake's native controls to ensure:
- Continuous visibility into every third-party integration connected to Snowflake — and into your IdP
- Real-time detection of credential misuse, bulk exports, and anomalous client activity
- Immediate alerting on persistence attempts and pre-exfiltration activity like masking policy removal
- Posture enforcement ensuring service accounts are network-restricted and integrations are inventoried
We recommend auditing your current Snowflake integration posture in Reco, enabling all relevant off-by-default alerts, and reviewing your IdP app data for third-party connections that may not be visible through Snowflake alone. Our team is here to help.

Cynthia Ardman
ABOUT THE AUTHOR
Cynthia is a Senior Threat Detection Engineer and CISSP at Reco. She is a former AWS security engineer with expertise in building detection and alerting systems that strengthen organizational resilience. Cynthia has deep hands-on experience with Splunk and incident response, and is driven by a passion for continuous improvement in the face of evolving threats.

Cynthia is a Senior Threat Detection Engineer and CISSP at Reco. She is a former AWS security engineer with expertise in building detection and alerting systems that strengthen organizational resilience. Cynthia has deep hands-on experience with Splunk and incident response, and is driven by a passion for continuous improvement in the face of evolving threats.



%201.svg)

-p-2000.png)








%201.svg)









.svg)